

Provide a rich, interactive and secure environment for accessing, creating, sharing, and discussing online information. Application examples include Intranets, Knowledge Management, eLearning, and Client Extranets.
Unicorn Software Solutions Portal and Social Collaboration solutions help organizations achieve a variety of business goals, such as better sharing of business intelligence, improved performance, and higher levels of innovation. By providing a single, comprehensive environment that connects diverse users, legacy processes, and disparate content types, we help our customers create valuable collaborative relationships that were previously impossible due to technical limitations. We extend proprietary applications, and connect people with information and each other regardless of operating system, network, or content type.
Unicorn Software Solutions Web Content Management solutions provide a rich environment for creating, managing, and publishing Web content, and an infrastructure for supporting multiple sites
Since the Web Content Management systems are built on Open Source platforms, supporting, managing, and expanding these systems is straightforward and cost-effective.
Because users of Web Content Management systems are generally non-technical business users or subject matter experts who are unfamiliar with HTML syntax, Unicorn Software Solutions include easy-to-use inline editors for text, HTML, and XML content, and connectors for editing documents using a variety of familiar desktop tools. For formatting simplicity, we include a transformation engine that converts content from one format to another. For example, incoming images of various types and sizes can be converted to a standard format and size. Drag-and-drop layout lets users customize the look and feel of a Web site without waiting for assistance from developers, and granular control over security enables content authors to secure web pages and the files, images, and videos embedded in them.
Unicorn Software Solutions Web Content Management solutions provide content management and search capabilities for over 35 languages, including the right-to-left languages such as Arabic and Hebrew. A robust full text search engine supports metadata and keyword searches, and returns results based on the user's access permissions.
A Digital Asset Management Software (DAM) is a single access point for all your rich digital media and its underlying metadata information throughout the extended enterprise.
Unicorn Software Solutions Open Source digital asset management system centralizes storage and provides easy, efficient, enterprise access to digital assets, and allows them to be quickly repurposed, which streamlines processes and saves money.
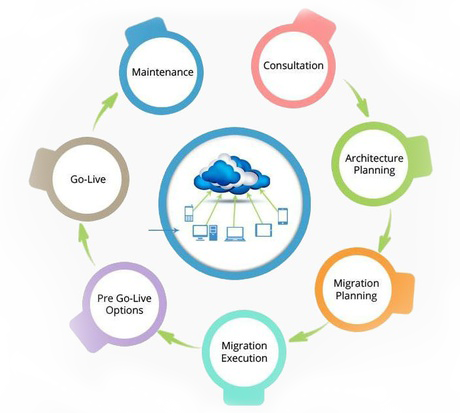
Unicorn has enabled more than 100 of its clients globally to cost efficiently migrate to new technologies while broadening the life cycle of their functionality rich existing legacy systems.
Projects include re-engineering software to migrate applications legacy systems to client/server architectures, to extend existing applications to the Internet, to migrate from existing applications to UNIX or Windows NT, or to update from a non-relational to a relational database technology.
Unicorn’s Application Security Solution establishes a continuous process that ensures security verification and remediation tasks are not only deployed across every stage of the SDLC, but also ingrained into the team's workflow.
Delivers an instant assessment of compliance to:
Each issue detected is prioritized, automatically correlated to the developer who introduced it, then distributed to his or her IDE with direct links to the problematic code and a description of how to remediate it. Eventually, developers start writing more secure code as a matter of habit.
Our centralized reporting system provides real-time visibility into overall security status and processes, documents improvements, and helps you determine what additional actions are needed to safeguard security.
Unicorn's policy-based approach establishes the organization's expectations for quality, leverages an automated infrastructure to ensure consistent, unobtrusive policy application, and automatically monitors policy compliance for visibility and auditability.
The extensive, continually-expanding knowledge base of rules can be easily customized (graphically, without coding) to enable automated monitoring of custom best practices. The result is more realistic and accurate validation that is aligned with the team's security priorities.
Unicorn establishes a continuous security process that ensures compliance tasks begin early and are deployed across every stage of the SDLC, as recommended by the PCI DSS. We've learned that even the best tool eventually becomes shelf ware if it is not integrated into a sustainable process. To ensure that the security process remains on track and does not disrupt project progress, Unicorn ingrains compliance tasks into the team's existing workflow and automates them so team members can focus on tasks that truly require human intelligence.
Get IT consulting services that address aspects of reducing cost, increasing agility and enabling transformation. Our consulting offerings are based on an analytical approach to understand the business problems, resulting in practical recommendation and actionable plans. Our value proposition is based on a confluence of business knowledge, deep hands-on technology skills and a focused approach through the use of in-house methodologies, frameworks and tools
Delivers an instant assessment of compliance to:
Make your IT infrastructure reliable and available with maximum uptime. With complex environments there is an increasing threat of security breaches too and managing the infrastructure with internal resources requires huge investment. We can help you align your business objectives with your infrastructure with scalable solutions.
We offer the following services in the Infrastructure Management Sector:
Unicorn has put together an impressive portfolio of QA and testing service offerings which are implemented to make sure that ISVs (Software Vendors) can deliver robust and dependable products to the market rapidly. Our services successfully address the usability, functionality, and performance testing aspects of the solution. We can help you with the entire product development life cycle ranging from the requirements phase, designing the test approach, tools selection, code reviews, building the test suites, test execution
